Lately there has been a new phishing trend where one url is creating thousands of phishing pages targeting many brands and customers. These new phishing attacks are created in a few seconds, and due to their quantity, are very difficult to take down.
1. The Redirection URL
For this attack to work, all parameters must be included in the URL. If only the domain is present it will generate a false 404 page. These URLs’ domains are all registered on Alibaba’s web services, and Google web hosting.
Thus, a working URL would look something like:
somedomain.top/ee11UX5BR1RkRHRnZEMIWBg1JnFVfVV4aQEgc1UkGxolUA8gSj83D0g_?cyr1636280111876
The website will then try to load a series of bots named anti1.php, anti2.php, etc. located at
/home/ somedomain /public_html/secure.alpha.gr2/index.php
The .top domain would retain the phished credentials from the attack at [domain].top/T_a_n_G_u_l_AR/alpha.txt
The bots would then forward the request to a remote address of a newly generated domain.
2. The Redirection
From this URL, a new domain is created to generate and host the new phishing attack on the middle redirect URL. From this example, the following page would look like:
http://7xhvqvpy.cn/eG4qV883/somedomain/static/sur.css
or
http://dmzyewzh.cn/8wLei2wf/somedomain/static/sur.css and other similar URLs.
This domain is on Cloudflare’s services in order to obfuscate the attack and keep fraud investigation at bay. The registrant’s information ties each of these domains back to peacchi@163.com, being created on March 18 2021. For example this domain:

Without the full URL, the attack will redirect elsewhere to a malicious website request to use notifications from the site. This is again to prevent investigation on the attack. The URL must be the same one as created in phase 1 or it will not work appropriately.
3. The Final Stage
Lastly, the attack loads the intended phishing page. In this example the URL is
http://7xhvqvpy.cn/eG4qV883/somedomain/?_t=1636993722wmx#1636993736735
The numbers in the parameter section of the URL changes with each time the page is refreshed, never leaving the exact same URL.

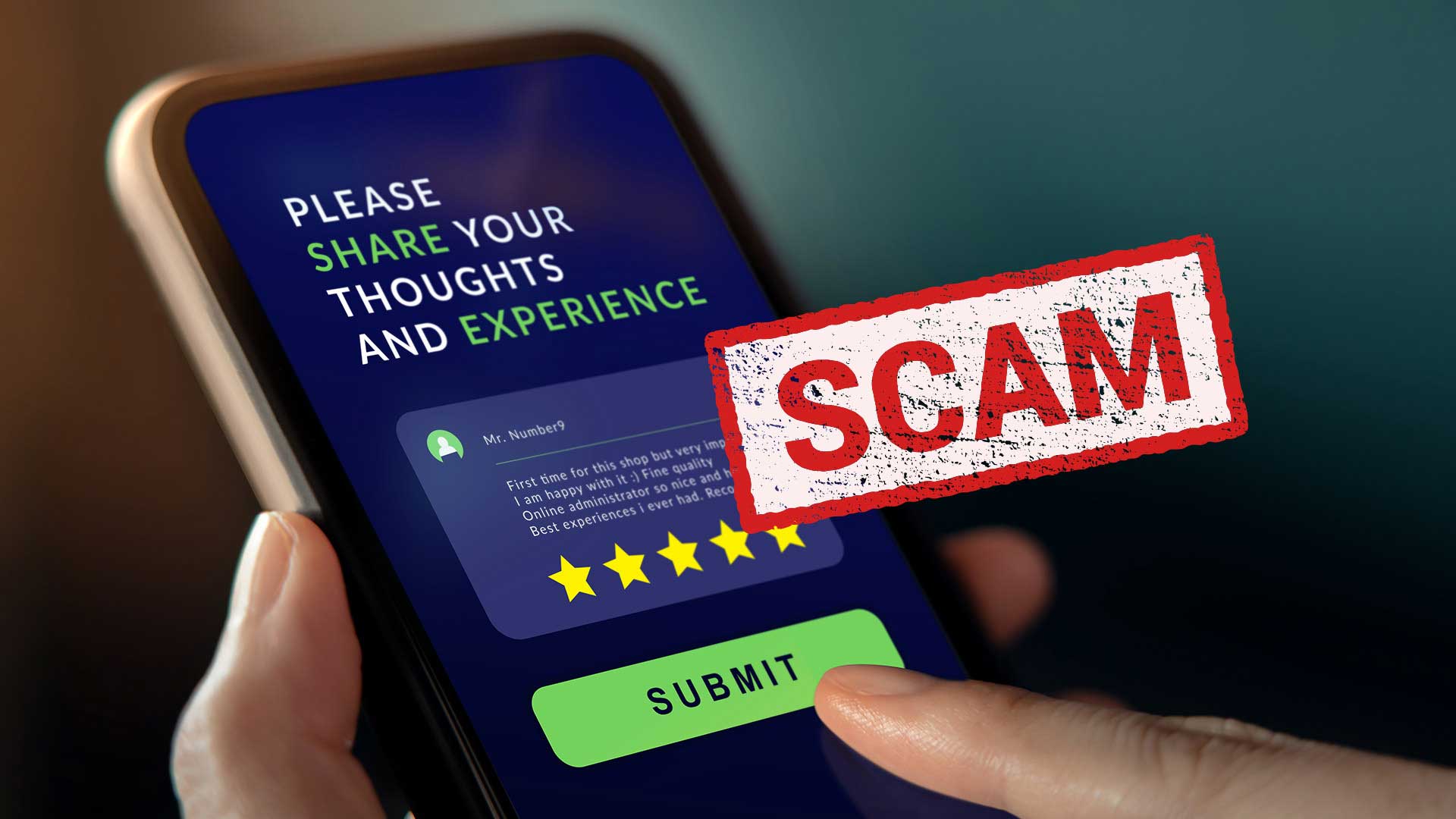
There is a fake survey that promises large amounts of money once the survey is completed, capturing sensitive information. The information is sent to the first URL where the credentials are stored.